Du kannst diesen Artikel auch auf Deutsch lesen.
Much work has been done to ensure that hardware wallets remain the safest way to store your Bitcoin. When it comes to external threats, like hackers and thieves, this has been achieved by various manufacturers.
But what if the threat is actually coming ‘from within’?
Is your money safe if the manufacturer of your hardware wallet is malicious or compromised?
Open Source does not automatically mean auditability
The firmware and bootloader of most hardware wallets are open source, meaning everyone can view it, build it and flash it onto their own device. The BitBox02 bootloaders can even present the firmware’s hash, to make sure it matches what you have compiled and flashed! Many people would argue that this means that the code cannot contain any backdoors and open-source software can therefore guarantee the integrity of the device.
This is only partially correct. In reality, verifying what is actually running on the chip is virtually impossible. There is no way to look into the chip and record everything it does. The chip might act completely normal and even show the correct firmware hash upon boot but run additional code that keeps a backdoor open.
Host device as a gatekeeper
Where open source really matters in terms of security is in regular software. The BitBoxApp and virtually any other hardware wallet companion app are open source. This is important because you can verify that the code you compile is the code you are running.
The companion app fulfils an important function here that might not be obvious at first glance: It acts as a gatekeeper for the information exchanged between the hardware wallet and the internet. Even if the hardware wallet runs malicious code to send your seed to the manufacturer, this would need its own code in the companion app and could easily be spotted by researchers. Especially when running a third-party application such as Sparrow or Electrum, it should be virtually impossible to share any unwanted data with another party.
But what if the wallet could somehow smuggle this data past the gatekeeper?
Leaking secrets with the “nonce covert channel attack”
When you send a bitcoin transaction, your wallet needs to create a signature. To create a signature, the wallet has to generate a random number, also called a “nonce”, which should be completely random and only used once. A malicious wallet can manipulate these nonces so that transactions can contain arbitrary data, such as parts of the seed. That means that the transaction it creates contains a hidden secret.
The companion app has no way of verifying that the chosen nonce is actually random or if it contains some hidden data. It will just receive a valid transaction from the hardware wallet and broadcast it.
Because transactions and signatures are recorded on the public blockchain, an attacker can look for these signatures and read out the secret contained in them. A few dozen transactions are enough to leak an entire master private key. Through this covert channel, a manufacturer could potentially collect the seeds of all its users over time without anyone noticing.
Anti-Klepto protocol
To solve this, Shift Crypto and Blockstream developed Anti-Klepto. Instead of solely relying on the randomness that the hardware wallet provides for the nonce, additional randomness is provided by the host device. This prevents the hardware wallet firmware from manipulating the nonce in a way so that it contains hidden data.
Before broadcasting a transaction, the companion app verifies that this randomness has actually been used to create the signature, eliminating the threat of leaking your seed.
We are currently developing Anti-Klepto support for Taproot addresses as their signatures differ from previous address types. To learn more about the details of how anti-klepto works, please read our previous blog post on the topic.
Conclusion
The threat of a malicious manufacturer might seem small, but when it comes to companies that might go out of business in the next decade, the possibility of pulling an “exit scam” should not be discounted. The fact that this attack is virtually impossible to prove as a victim could provide additional motivation for malicious actors.
As hardware wallets are mainly used for the long-term storage of Bitcoin, Anti-Klepto provides the user with additional peace of mind in an adversary environment. To date, the only hardware wallets that have implemented the Anti-Klepto protocol are the BitBox02 and the Blockstream Jade.
We strongly encourage other manufacturers to implement this open-source protocol to show their willingness to secure their users' funds.
Can a hacker steal my Bitcoin using manipulated nonces?
This attack needs a malicious (or compromised) hardware wallet manufacturer. If someone breaks into your computer, there is no way for them to exploit this attack vector.
Are my Bitcoins safe?
It's hard to prove that this attack has been used in the past. Since the attack needs a few dozens signatures to work, wallets that have not been used to send many transactions should be safe.
How can I use Anti-Klepto?
Wallets that have Anti-Klepto implemented use it automatically for every supported transaction. Since it's integrated into HWI, Anti-Klepto is also used when you are interacting with a third party wallet, such as Electrum.
Which wallets support Anti-Klepto?
The Anti-Klepto protocol is currently only supported by the BitBox02 and the Blockstream Jade.
Don’t own a BitBox yet?
Keeping your crypto secure doesn't have to be hard. The BitBox02 hardware wallet stores the private keys for your cryptocurrencies offline. So you can manage your coins safely.
The BitBox02 also comes in Bitcoin-only version, featuring a radically focused firmware: less code means less attack surface, which further improves your security when only storing Bitcoin.
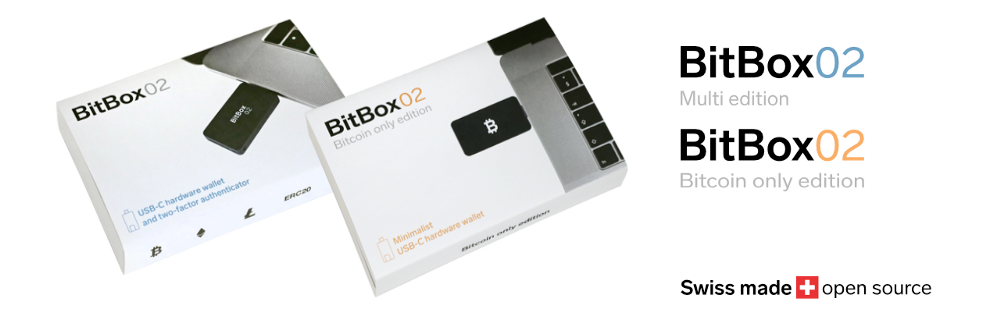
Shift Crypto is a privately-held company based in Zurich, Switzerland. Our team of Bitcoin contributors, crypto experts, and security engineers builds products that enable customers to enjoy a stress-free journey from novice to mastery level of cryptocurrency management. The BitBox02, our second generation hardware wallet, lets users store, protect, and transact Bitcoin and other cryptocurrencies with ease - along with its software companion, the BitBoxApp.